-->
Note: Since July 28, 2016, all new device models, lines or series (or if you are updating the hardware configuration of a existing model, line or series with a major update, such as CPU, graphic cards) must implement and enable by default TPM 2.0 (details in section 3.7 of the Minimum hardware requirements page). The requirement to enable TPM 2.0 only applies to the manufacturing of new devices.
Trusted Platform Module (TPM) technology is designed to provide hardware-based, security-related functions. A TPM chip is a secure crypto-processor that helps you with actions such as generating, storing, and limiting the use of cryptographic keys. Many TPMs include multiple physical security mechanisms to make it tamper resistant, and malicious software is unable to tamper with the security functions of the TPM.
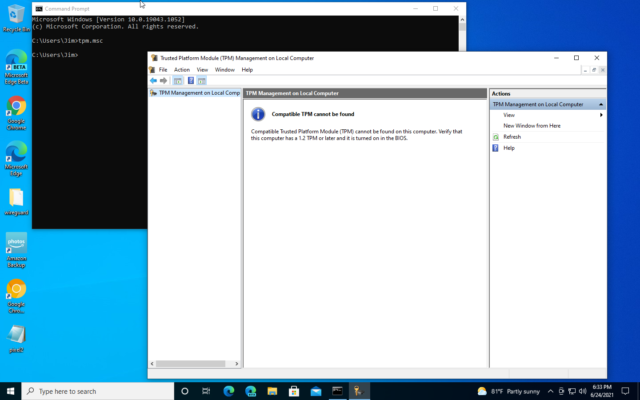
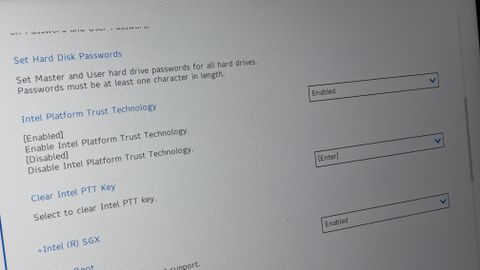
To enable the Trusted Platform Module (TPM) on your computer through the Windows 10 settings, use these steps: Warning: Changing the incorrect firmware settings can prevent your device from. Sep 16, 2021 TPM 2.0 support available on all Commercial platforms in Spring 2016, and the factory default TPM mode on Windows 10 is TPM 2.0. All new Windows 10 machines will need to have TPM 2.0 enabled by default this summer. Driver epson v750 pro for Windows 7 x64 download. I see Security Devices as Trusted Platform Module TPM 2.
Traditionally, TPMs have been discrete chips soldered to a computer’s motherboard. Such implementations allow you as the original equipment manufacturer (OEM) to evaluate and certify the TPM separate from the rest of the system. Some newer TPM implementations integrate TPM functionality into the same chipset as other platform components while still providing logical separation similar to discrete TPM chips.
TPMs are passive: they receive commands and return responses. To realize the full benefit of a TPM, you must carefully integrate system hardware and firmware with the TPM to send it commands and react to its responses. TPMs provide security and privacy benefits for system hardware, platform owners, and users.
Before it can be used for advanced scenarios, however, a TPM must be provisioned. Starting with Windows 10, the operating system automatically initializes and takes ownership of the TPM. That means that IT professionals should not have to configure or monitor the system.
For more information about the specific requirements that must be met, see System.Fundamentals.TPM20.
IT Professionals: To understand how TPM works in your enterprise, see Trusted Platform Module.
Related topics
Acer PCGuard
Providing the ultimate computer protection, Acer Veriton computers feature the instant recovery solution: PCGuard. Using the latest recovery technology, PCGuard allows users to recover an entire system to a preset status within seconds. This technology is perfect for public-use computers, such as in a classroom or internet café, and represents the best protection against viruses, malware and misuse.
PCGuard. Using the latest recovery technology, PCGuard allows users to recover an entire system to a preset status within seconds. This technology is perfect for public-use computers, such as in a classroom or internet café, and represents the best protection against viruses, malware and misuse.Instant Recovery
This revolutionary solution allows a PC to be reset to a preset state within seconds. This feature ensures that no matter what happens to your Veriton computer, no matter who is using it, the settings and programs can be recovered fast. Have a class and reset all PCs to your defined default within a minute's time. Recover your IT café's virus ridden machine before your customer can complain. Give patients a stable environment to fill-in necessary information or order prescriptions. Whatever the situation, PCGuard's instant recovery keeps you secure.
Net Clone
Distribute licensed software and perform mass installations via Net Clone. This handy software allows computers with PCGuard to copy an entire hard drive across a network for fast installation of important software. Using a common local network LAN, users can install a software package – such as Office, anti-virus software, and more - on a single computer and then copy the environment across a LAN for fast setup of an entire network.
Network managementMake changes to an entire network via a single computer. Acer PCGuard's network management function allows an administrator to setup and enforce systems' shutdown, recover, and copy system information. With this powerful software the admin, or teacher/café owner, may ensure that users cannot permanently change the preset settings or software.
Acer Security Suite
The Acer Security Suite is a complete hardware and software package that is designed to protect your company's assets from harm and theft. This powerful solution encrypts any program file, computer, and user-set passwords and can leverage TPM technology for totally secure computing.Solid Security

 Utilizing a trusted platform module (TPM) available on select Acer Veriton computers, this total solution creates and stores a password for your PC on the chipset. Separate from the hard-drive, the chipset is safe from common viruses, spyware, and trojans which infect and steal computers' information.
Utilizing a trusted platform module (TPM) available on select Acer Veriton computers, this total solution creates and stores a password for your PC on the chipset. Separate from the hard-drive, the chipset is safe from common viruses, spyware, and trojans which infect and steal computers' information.
Sophisticated management
Acer Security Suite's software interface offers users an intuitive window to their computer's passwords, encryptions, and documents. Quickly accessible via Veriton ControlCenter, this powerful suite offers a centralized interface to:
Trusted Platform Module 2.0 Driver Windows 10 Dell
Trusted Platform Module Windows 10 Download
- Manage security policies and user security settings with a consolidated, one-stop security center. Security wizards assist the user with first time setup, multi-step tasks, and adding TPM security to common applications.
- Combine authentication methods, such as passwords, TPM certificates, smart cards and fingerprints, for multi-level security on Windows®, wireless networks, secure applications and more
- Protect any type of file via a secure virtual drive. Acting like a separate hard-drive, the secure virtual drive stores all your files and documents in a single, encrypted location that leverages existing hard drive or network space.
- Enjoy speedy access to secure websites and applications with automated features for saving and supplying passwords.